When one breach can cascade into chaos, your presentations need to armor up with clarity and conviction. The System Access PowerPoint Template arms telecom pros, risk analysts, and corporate sentinels with 28 fortified diagrams across seven defensive color sets, dissecting vulnerabilities from electronic ledgers to paperless perils. It`s the shield for those briefing on system safeguards, turning outage hypotheticals into hardened strategies.
Tailored for PowerPoint 2016 and beyond, featuring three masters and backgrounds that evoke fortified perimeters, it integrates into your defense playbook seamlessly. Kick off with a master outlining threat landscapes, then fortify with visuals that layer protections logically.
Fortified Foundations: Template Strongholds
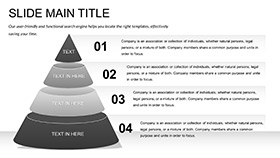
Diagrams here are battle-tested: The access tier pyramid (slide 13) tiers privileges visually - escalate levels with drag fills, illuminating escalation risks at a pyramid`s peak.
- Resilient Renderings: Firewall flows and VPN vaults rendered in scalable strokes.
- Palette Protections: Muted earths for risk maps, alert reds for breach alerts.
- Sentry Supports: Hyperlink hotspots for drill-down to policy docs.
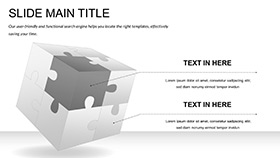
A bank auditor fortified a compliance audit with the failover cluster (diagram 23), clustering nodes to cluster contingencies, averting audit alarms through visual vigilance.
Mastering the Moats: Layout Layers
Masters span alert-heavy for warnings, neutral for overviews, and archival for logs. Backgrounds shift from barred grids to veiled veils, adjustable via theme colors for alert harmony.
Defending Domains: Tactical Terrains
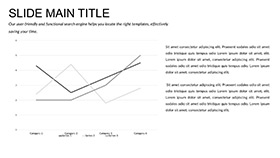
Risk managers mapping LAN labyrinths use the topology tracer (slide 8), tracing cables to trace chokepoints - animate traces to replay outage origins.
One: Load network XML, two: Route paths, three: Sequence reveals, four: Note failure fixes.
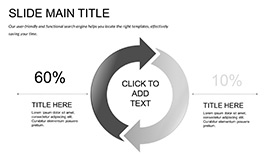
For payment pros probing electronic flows, the transaction shield (diagram 18) shields steps with barrier icons, as one did to shield transaction trails in fraud forums.
Workflow Warriors and Breach Briefers
Workflow wardens sequence the approval chain (slide 5), chaining locks for multi-factor mandates, chaining consensus without chain reactions.
- Bind to Active Directory for role pulls.
- Cluster for reusable segments.
- Simulate in reading view for flow checks.
Corporate crisis teams layer the recovery roadmap (diagram 28), roadmapping restores to roadmap resilience.
Armored Against Amateurs
Superior to scattershot shapes, these include conditional formatting for dynamic risks and zoom sections for deep defenses. Cloud-sync for sentinel shares keeps guards aligned.
Envision slides that don`t just report risks - they repel them, rallying readiness.
Vigilance Vectors
Tag notes: "Pyramid depicting role-based access tiers." Invoke variants for slide variants.
Fortify forward - grab this template for $22 and access assurance.
Frequently Asked Questions
Focus on telecom or general IT?
Balanced for both, with telecom tilts in flow diagrams.
Customizable barriers?
Vector barriers bend to your protocols precisely.
LAN failure sims?
Yes, with path breaks for failure foresight.
Color for alerts?
Scheme swaps flag urgencies automatically.
Export for reports?
High-res PNGs and locked PDFs ready.