Download the Cybersecurity PowerPoint Template with 28 fully editable diagrams in 7 color schemes. Designed for IT professionals to present threat analysis, network protection, and digital defense strategies using Microsoft PowerPoint files. Instant download includes PPTX, POTX, and JPG formats for immediate use.
What's Included
The Cybersecurity PowerPoint Template delivers a complete package of 28 professional diagrams prepared specifically for cybersecurity topics. You receive the primary PPTX file for direct editing, a POTX theme file for consistent styling across your decks, and JPG preview images for planning. All elements are supplied in the download for product ID 13935 under the Computer - IT category.
These 28 diagrams are accompanied by exactly 7 color schemes that let you switch appearances with a single click. The files support full editing in Microsoft PowerPoint on Windows or Mac without additional software. This set addresses the exact needs of users who want ready cybersecurity visuals rather than starting with blank slides.
File Format Breakdown
PPTX files contain the editable diagrams while POTX provides the master theme. JPGs serve as quick references so you can select the right visual before opening the main file. The entire package is structured for instant integration into existing presentations or new builds focused on security narratives.
Key Features
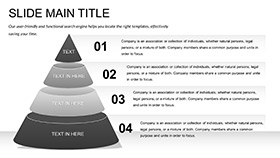
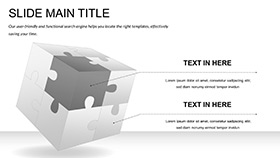
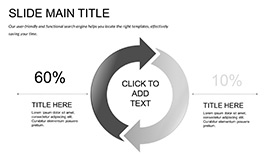
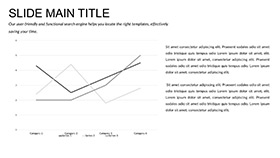
This template stands out with its 28 diagrams built around cybersecurity themes such as threat detection and protection layers. The 7 color schemes offer flexibility for different corporate branding or audience types. All shapes, text, and icons remain fully vector-based and editable.
Editable Components
Text placeholders, color fills, and shape outlines can be modified individually. Icons scale without distortion and layers stay intact during edits. These features ensure the diagrams fit any presentation length or complexity level required by IT teams.
| Feature | This Template | Building From Scratch |
|---|
| Diagrams Included | 28 | 0 |
| Color Schemes | 7 | 1 |
| File Formats | PPTX, POTX, JPG | None |
| Vector Editing | Yes | Manual creation |
| Compatibility | PowerPoint 2010+ | Time intensive |
| Theme Application | POTX ready | Custom build |
Professional Use Cases
Boardroom Threat Reporting
A CISO at a regional bank used the diagrams from this Cybersecurity PowerPoint Template to map out ransomware attack paths and layered defenses during an executive briefing. The visual structure clarified complex concepts for non-technical board members and resulted in immediate approval for additional security tooling investments.
Training Sessions for Teams
An IT security trainer at a healthcare provider incorporated the 28 diagrams into monthly compliance workshops. Participants could follow the step-by-step protection visuals, improving retention of procedures and reducing reported incidents by providing clear reference materials during the sessions.
How to Customize
Step-by-Step Workflow
Download the package and extract the files. Open the PPTX in Microsoft PowerPoint and select one of the 7 color schemes from the variants. Replace placeholder text with your specific threat data or compliance metrics. Adjust shape colors or icon layers to align with company branding guidelines. Save the customized file and export as PDF for distribution or present directly from PowerPoint.
This process takes minutes rather than hours because the diagrams already contain structured layouts for cybersecurity topics. The POTX file lets you apply the same styling to other slides in your deck for uniform appearance.
Why Choose This Template
The Cybersecurity PowerPoint Template differentiates from related products on the site such as the Cyber Security and Cybercrime PowerPoint Template by concentrating on defense fortification visuals rather than crime-focused narratives. The inclusion of 7 color schemes provides more branding flexibility than single-scheme alternatives listed in the related section.
Compared to designing 28 diagrams manually, this set delivers consistent professional quality and saves hours of design work while maintaining vector scalability for any screen size or print requirement.
Is the Cybersecurity PowerPoint Template compatible with older versions of PowerPoint?
Yes, the 28 diagrams open and edit correctly in Microsoft PowerPoint 2010 and every subsequent version on both Windows and Mac systems. The vector shapes and color schemes remain intact without conversion errors. You can apply the POTX theme to legacy files for consistent styling across mixed-version environments. This compatibility ensures that teams with varying software setups can still use the full set of diagrams for threat analysis or training materials without technical barriers.
How do I edit the diagrams and apply different color schemes?
The diagrams contain fully selectable text placeholders, shape fills, and icon layers that you modify directly in PowerPoint. To change color schemes, simply switch the variant slide or apply the built-in theme from the 7 options. No external plugins are required. This level of control allows security analysts to customize icons for specific tools like firewalls or encryption while keeping the overall layout professional and consistent for any presentation length.
What licensing is included with this Cybersecurity PowerPoint Template?
The download grants standard commercial and personal use rights for presentations, reports, and training materials. You may incorporate the 28 diagrams into client deliverables or internal company decks without additional fees. Attribution is not required. This license covers the exact use cases of IT consultants and CISOs who present security strategies to stakeholders or regulators.
Can I use the diagrams in both digital and printed formats?
Yes, the vector-based diagrams retain sharpness at any size for screen projections, PDF exports, or printed handouts. The 7 color schemes adapt to both light and dark printing conditions without loss of detail. Security teams frequently print the diagrams as reference posters or include them in compliance reports where high-resolution output is mandatory.
What happens after I complete the download?
You receive an immediate link to the zip package containing all PPTX, POTX, and JPG files. Unzip and open the main file to begin editing the 28 diagrams right away. No account or additional steps are needed. This instant access lets cybersecurity professionals prepare last-minute briefings or training sessions without delay.